Migration of Exchange can be a complex, challenging and stressful task. It needs in-depth knowledge on Exchange and all the system connected to Exchange. Also, need to make sure the users are not affected during the migration with no data loss.
Kernel Migration helps to migrate Exchange mailboxes from one version of Exchange to another. Weather it can be a cross forest migration or migration from on premises to a hosted solution or even to your tenant in office 365. This tool supports all version of Exchange starting from Exchange Server 2000 to Exchange Server 2016, and hopefully, it support Exchange server 2019 migration soon as well. Kernel Migrator for Exchange is a clean and comfortable to use interface to make complete process more comfortable and have a controller over it.
In addition to mailbox migration Kernel Migration tool helps to perform the below:
· Pre-Migration Analysis.
· Public folder migration
· Global Address Book (GAL) Sync.
· Migrate outlook Rules
· Update outlook profile when mailbox is migrated.
· Reporting
· Migration cleanup
· Rollback Mailbox migration
· Rollback public folder migration
· Rollback GAL sync
Pre-Migration Analysis
Pre-Migration Analysis is to estimate the time it takes for migration. It helps to plan the migration and allow no or limited imaged to the end users. It allows to estimate the both the time for mailbox and the public folder data.
Public folder migration
Public folder migration can be tricky and complicated. Native scripts officering from Microsoft is manual and complex. This tool helps to migration the public folder data migration and also easily migration the public folder permission.
Global Address Book (GAL) Sync
GAL Sync is used when Exchange Cross forest migration performed. It helps to sync all the mail accounts from the source forest to the target Exchange forest as mail contacts. This tool can be used for GAL Sync as well to sync the email objects from both the forest as mail contacts. This helps to see the users from other forest users in their local address book. It also offers excellent control on the objects it can sync and exclude.
Migrate outlook Rules
Local Outlook Rules can also be uses to migrate from the source to the Target outlook. This option helps to have no or minimum action from the users end when the mailbox migrated.
Rollback
Rollback option is a great benefit which we can make use when we need it. Migration can many times leads to a rollback due to various reason. We should always be in a position to rollback to a state which was before. Kernel migrator for Exchange offers to rollback mailbox migration, public folder migration and also GAL sync objects.
Let’s see how simple is to migration mailbox from on-prem to office 365 using Kernel Migrator for Exchange.
1. Install the Kernel migration on the source forest Exchange server
2. Start the Kernel migration for Exchange -> click on Add project -> provide a Project Name.
3. Click on Add Job for Mailbox -> select the Project then provide the appropriate name and click Next
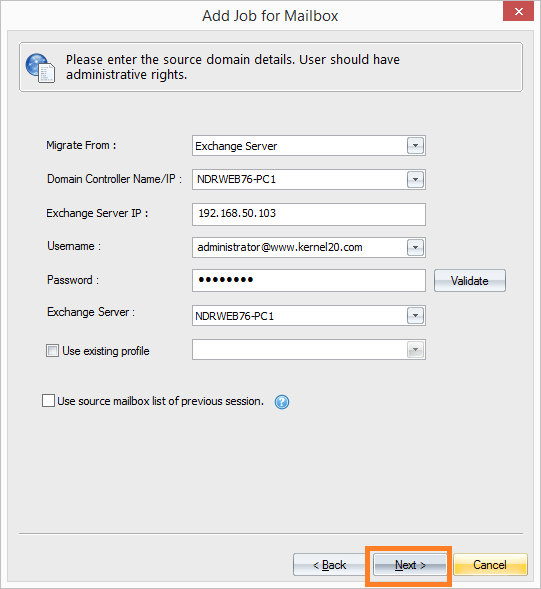
4. Select Migrate from Exchange Server then provide the Domain controller and other necessary details followed by the administrator account having full mailbox permission for each source mailboxes and click NEXT
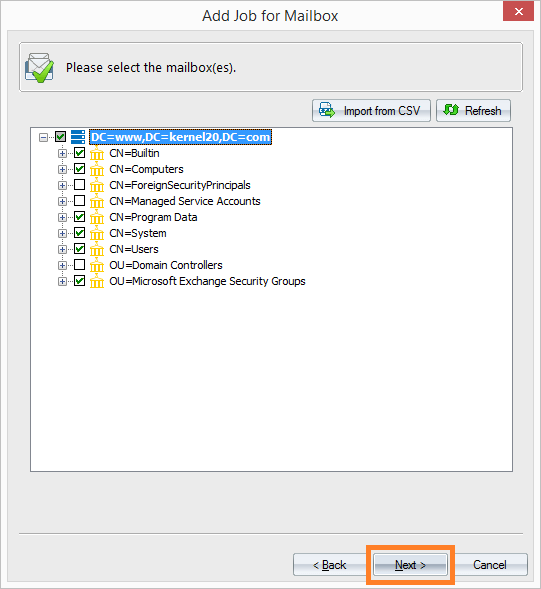
5. In the next page slect the mailboxes which you wanted to migrate. You can drill down the OU where you have the users, or you can select the users which needs to migrate. We can also import CSV file with the list of mailbox to migrate.
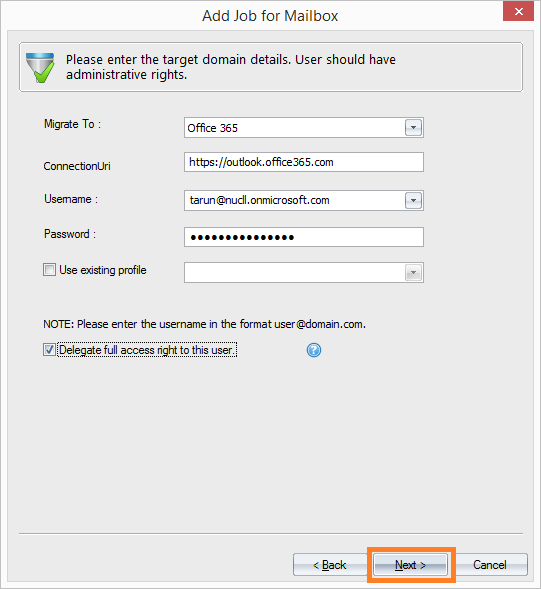
6. In the next page, select migrate to Office 365 then provide the office 365 admin account credentials and click Next
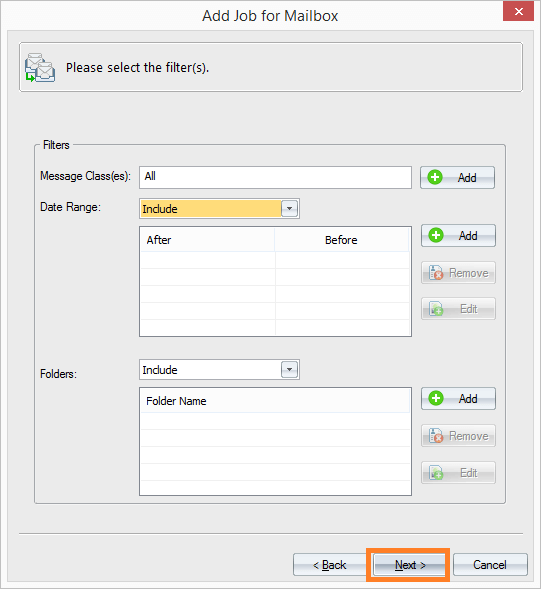
7. This page is add any exception to migration content. By default, full mailbox is migrate. Select Next to continue with the next page.
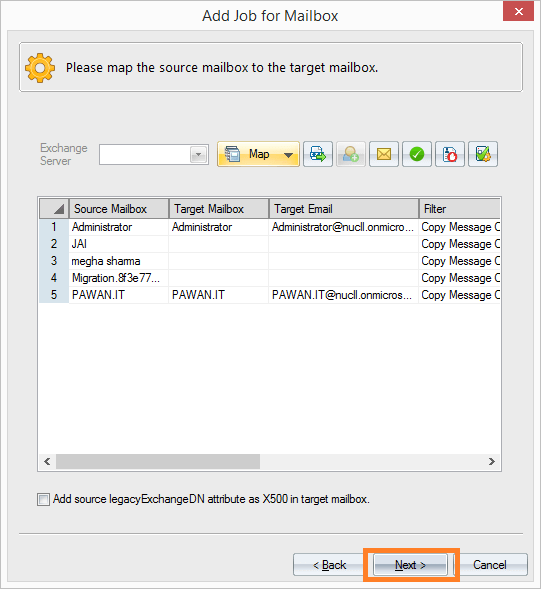
8. Now select the corresponding source and target mailbox, so that content migrated to the correct target mailbox and click Next
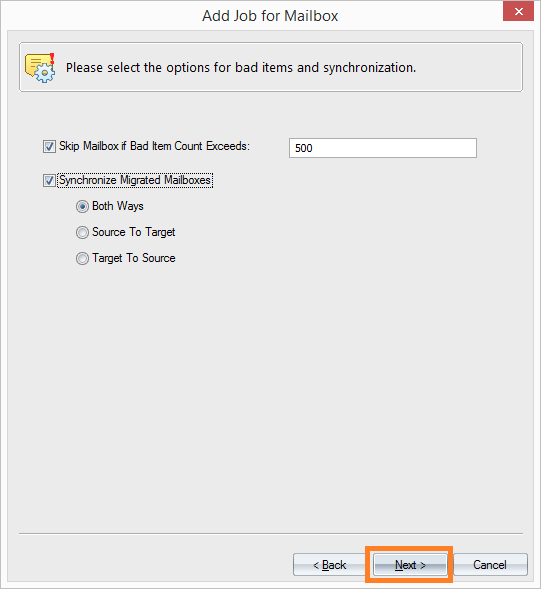
9. Specify the Bad item limit which it can ignore before the migration fails then specify the how the mailbox content to synced between source and target mailboxes. Then click Next to continue
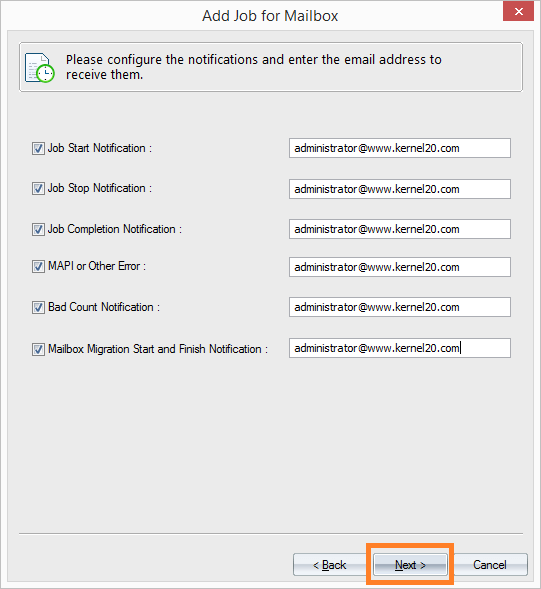
10. Provide the email address of the engineer who need to get the migration status update notification and click Next to continue
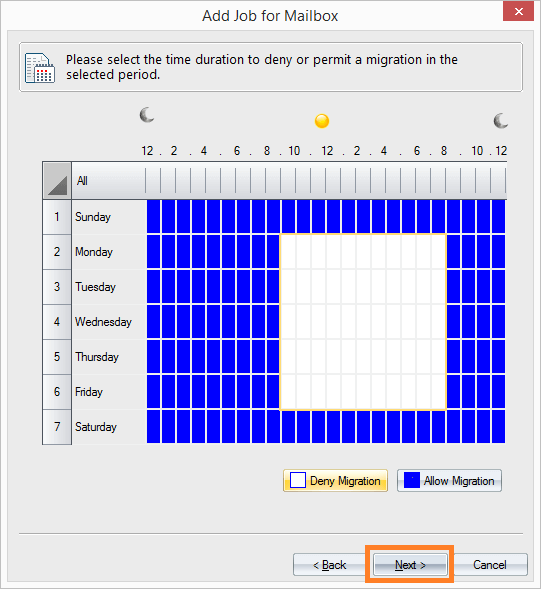
11. Select the time when the mailbox sync to happen. To avoid any mailbox sync in the working hours and also to save the network bandwidth.
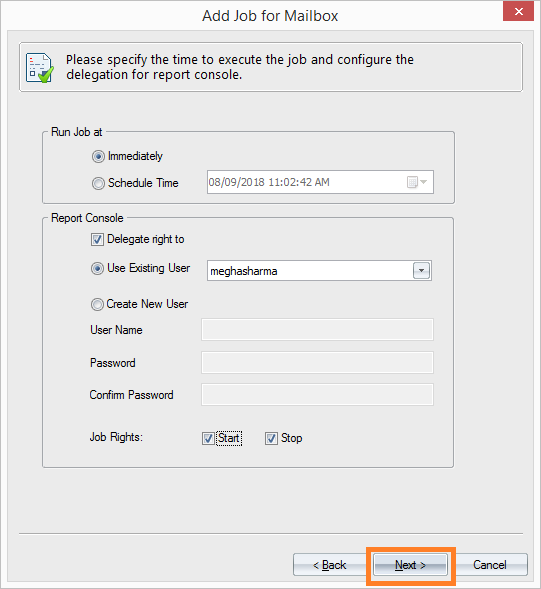
12. Scheulde the sync when you wanted to start and also allows option to configure who should get detailed migration report. Click Next to create the migration Job.
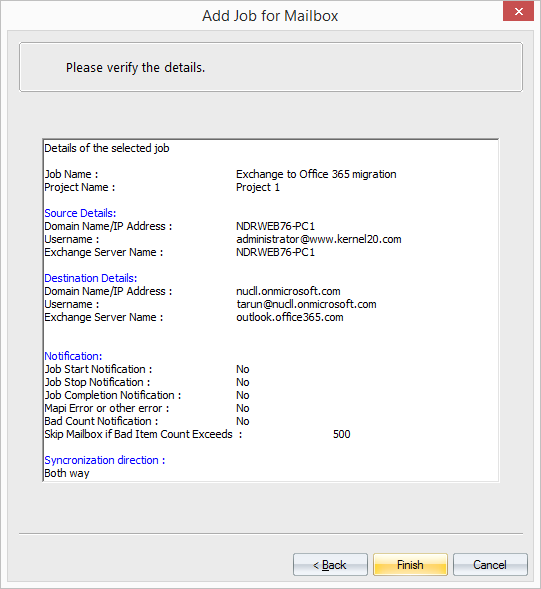
13. The final configuration page provides detailed summary of all the configuration selected and allow us to validate. Based on the selection name, Kernel Migrator performs the migration.
Conclusion:
Kernel Migration for Exchange is clean and easy to use tool. It reduces the efforts and time for the Exchange administrator with minimum impact to the end users. It also provides detailed report to the administrator and other necessary alerts when any issues occur. It allows administrator to have great control over the migration which native migration tool does not offer. Certainly, would recommend this tool for the user’s migration from onprem to office 365.